Download Oracle.1z0-820.TestKing.2018-12-10.75q.tqb
| Vendor: | Oracle |
| Exam Code: | 1z0-820 |
| Exam Name: | Upgrade to Oracle Solaris 11 System Administrator |
| Date: | Dec 10, 2018 |
| File Size: | 2 MB |
Demo Questions
Question 1
You need to update an OS image on a client. The pkg publishers command displays the wrong publisher with the wrong update:
PUBLISHER TYPE STATUS URI
Solaris origin online http://pkg.oracle.com/solaris/release
The update is available on the updated publisher:
PUBLISHER TYPE STATUS URI
Solaris origin online http://sysA.example.com
Select the option that describes the procedure used to update the OS image on the system from the updated publisher.
- Copy the repository from the ISO image onto the local client.Configure the repository on the client by using the svccfg - s command so that the Solaris publisher is connected to the new repository.Refresh the application/pkg/server service.Issue the pkgrepo refresh command to refresh the repository catalog
- Configure the publisher on the client using the svcfg - s command so that the Solaris publisher is connected to the repository at http://sysA.example.comRefresh the application/pkg/server service.Issue the pkgrepo refresh command to repository catalog
- Use the pkg set-publisher command to change the URL of the publisher Solaris to http://sysA.example.com.Issue the pkg update command to update the OS image.
- Add the new publisher http://sysA.example.com SolarisUse the pkg set-publisher command to set the publisher search order and place http://sysA.example.com of http://pkg.oracle.com/solaris/releaseIssue the pkg publisher command to view the publishers.Set the new publisher to sticky.Issue the pkg update command to update the OS image.
Correct answer: C
Explanation:
You can use the pkg set-publisher command to change a publisher URI. Changing a Publisher Origin URI To change the origin URI for a publisher, add the new URI and remove the old URI. Use the -g option to add a new origin URI. Use the -G option to remove the old origin URI. # pkg set-publisher -g http://pkg.example.com/support \-G http://pkg.example.com/release example.comNote: You can use either the install or update subcommand to update a package.The install subcommand installs the package if the package is not already installed in the image. If you want to be sure to update only packages that are already installed, and not install any new packages, then use the update subcommand. Reference: Oracle Solaris 11 Express Image Packaging System Guide, Managing Package Publishers You can use the pkg set-publisher command to change a publisher URI.
Changing a Publisher Origin URI
To change the origin URI for a publisher, add the new URI and remove the old URI. Use the -g option to add a new origin URI. Use the -G option to remove the old origin URI.
# pkg set-publisher -g http://pkg.example.com/support \
-G http://pkg.example.com/release example.com
Note: You can use either the install or update subcommand to update a package.
The install subcommand installs the package if the package is not already installed in the image. If you want to be sure to update only packages that are already installed, and not install any new packages, then use the update subcommand.
Reference: Oracle Solaris 11 Express Image Packaging System Guide, Managing Package Publishers
Question 2
Alice is a user account used by Alice on a Solaris 11 system.
sadmin is a role account on the same system.
Your task is to add the command /usr/sbin/cryptoadm to the Network management profile, so that Alice can execute it, while assuming the sadmin role.
Select the three activities necessary to accomplish this.
- To the file /etc/security/prof_attr, add the line:Network Management: solaris:cmd:RO::/usr/sbin/cryptoadm:euid=0
- To the file /etc/security/auth_attr, add the line:Network Management: solaris:cmd:RO::/usr/sbin/cryptoadm:euid=0
- To the file /etc/security/exec_attr.d/local-entriies, add the line:Network Management: solaris:cmd:RO::/usr/sbin/cryptoadm:euid=0
- Run the roles alice to ensure that alice may assume the role sadmin.
- Run the command profiles sadmin to ensure that the role sadmin includes the network Management profile.
- Run the command profiles alice to ensure that the Alice has permissions to access the Network management profile.
- Run the command profiles “Network management” to ensure that the Network management profile includes the sadmin role.
Correct answer: CDG
Explanation:
C: /etc/security/exec_attr is a local database that specifies the execution attributes associated with profiles. The exec_attr file can be used with other sources for execution profiles, including the exec_attr NIS map and NIS+ table. A profile is a logical grouping of authorizations and com- mands that is interpreted by a profile shell to form a secure execution environment. Incorrect answers: A: etc/security/prof_attr is a local source for execution profile names, descriptions, and other attributes of execution profiles. The prof_attr file can be used with other profile sources, including the prof_attr NIS map. B: /etc/security/auth_attr is a local source for authorization names and descriptions. The auth_attr file can be used with other authorization sources, including the auth_attr NIS map and NIS+ table. An authorization is a right assigned to users that is checked by certain privileged programs to determine whether users can execute restricted functionality. Reference: man exec_attr C: /etc/security/exec_attr is a local database that specifies
the execution attributes associated with profiles. The
exec_attr file can be used with other sources for execution
profiles, including the exec_attr NIS map and NIS+ table.
A profile is a logical grouping of authorizations and com-
mands that is interpreted by a profile shell to form a
secure execution environment.
Incorrect answers:
A: etc/security/prof_attr is a local source for execution profile names, descriptions, and other attributes of execution profiles. The prof_attr file can be used with other profile sources, including the prof_attr NIS map.
B: /etc/security/auth_attr is a local source for authorization names and descriptions. The auth_attr file can be used with other authorization sources, including the auth_attr NIS map and NIS+ table.
An authorization is a right assigned to users that is checked by certain privileged programs to determine whether users can execute restricted functionality.
Reference: man exec_attr
Question 3
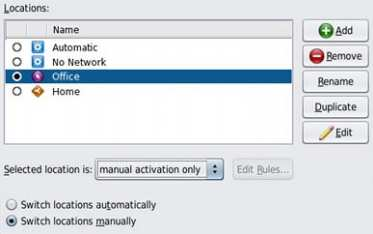
Select the two statements that correctly describe the operation of NWAM.
- If a location is explicitly enabled, it remains active until explicitly changed.
- Wireless security keys can be configured by using the nwammgr command.
- NWAM stores profile information in /etc/ipadm/ipadm.conf and /etc/dladm/datalink.conf.
- Multiple locations may be automatically activated in systems with multiple network interface cards.
- Interface NCU Properties "float" and are automatically attached to the highest priority Link NCU Property.
- If the DefaultFixed NCP is enabled, persistent configuration, stored in /etc/ipadm.conf and /etc/dladm/datalink.conf is used.
Correct answer: AD
Explanation:
A: Conditional and system locations can be manually activated, which means that the location remains active until explicitly disabled.D: A location comprises certain elements of a network configuration, for example a name service and firewall settings, that are applied together, when required. You can create multiple locations for various uses. For example, one location can be used when you are connected at the office by using the company intranet. Another location can be used at home when you are connected to the public Internet by using a wireless access point. Locations can be activated manually or automatically, according to environmental conditions, such as the IP address that is obtained by a network connection. Incorrect answers:Note: The Network Auto-Magic (NWAM) feature simplifies basic network configuration by automatically addressing basic Ethernet and WiFi configurations, such as connecting to your wired or wireless network at startup and displaying notifications about the status of your currently active network connection from the desktop. NWAM is also designed to simplify some of the more complex networking tasks, such as the creation and management of system-wide network profiles, for example, the configuration of name services, IP Filter and IP Security (IPsec). Reference: Oracle Solaris Administration: Network Interfaces and NetworkVirtualization, Activating and Deactivating ProfilesReference: Oracle Solaris Administration: Network Interfaces and NetworkVirtualization,Creating and Managing Locations A: Conditional and system locations can be manually activated, which means that the location remains active until explicitly disabled.
D: A location comprises certain elements of a network configuration, for example a name service and firewall settings, that are applied together, when required. You can create multiple locations for various uses. For example, one location can be used when you are connected at the office by using the company intranet. Another location can be used at home when you are connected to the public Internet by using a wireless access point. Locations can be activated manually or automatically, according to environmental conditions, such as the IP address that is obtained by a network connection.
Incorrect answers:
Note: The Network Auto-Magic (NWAM) feature simplifies basic network configuration by automatically addressing basic Ethernet and WiFi configurations, such as connecting to your wired or wireless network at startup and displaying notifications about the status of your currently active network connection from the desktop.
NWAM is also designed to simplify some of the more complex networking tasks, such as the creation and management of system-wide network profiles, for example, the configuration of name services, IP Filter and IP Security (IPsec).
Reference: Oracle Solaris Administration: Network Interfaces and NetworkVirtualization, Activating and Deactivating Profiles
Reference: Oracle Solaris Administration: Network Interfaces and NetworkVirtualization,Creating and Managing Locations






