Download Oracle.1z0-460.CertDumps.2018-07-04.40q.tqb
| Vendor: | Oracle |
| Exam Code: | 1z0-460 |
| Exam Name: | Oracle Linux 6 Implementation Essentials |
| Date: | Jul 04, 2018 |
| File Size: | 520 KB |
| Downloads: | 1 |
Demo Questions
Question 1
Identify the option with two files that are found in the /etc/sysconfig directory.
- /etc/sysconfig/autofs and/etc/sysconfig/authconfig
- /etc/sysconfig/ifcfg-eth0 and/etc/sysconfig/atd
- /etc/sysconfig/resolv.conf and/etc/sysconfig/network
- /etc/sysconfig/resolv.conf and/etc/sysconfig/grub.conf
Correct answer: A
Explanation:
* The /etc/sysconfig/autofs file defines custom options for the automatic mounting of devices. * The /etc/sysconfig/authconfig file sets the kind of authorization to be used on the host. Note: * /etc/sysconfig/networkUsed to configure networking options. Incorrect:Not C, Not D: * The program that resolves hostnames to IP addresses reads a file called resolv.conf. This file is located in /etc/resolv.conf directory. * The /etc/sysconfig/autofs file defines custom options for the automatic mounting of devices.
* The /etc/sysconfig/authconfig file sets the kind of authorization to be used on the host.
Note: * /etc/sysconfig/network
Used to configure networking options.
Incorrect:
Not C, Not D:
* The program that resolves hostnames to IP addresses reads a file called resolv.conf.
This file is located in /etc/resolv.conf directory.
Question 2
Which two options can be completed when using the Firewall Configuration Tool, system – config – firewall?
- Write complex firewall rules for checking, logging, and rejecting inbound and outbound connections
- Enabling or disabling the firewall entirely
- Build a filter to obfuscate sensitive data (national ID numbers, Credit Cards, and so on)
- Select the services that have access to the network resource
Correct answer: BC
Explanation:
system-config-firewall The GUI screen to control the firewall is available from the menu (System > Administration > Firewall) or can be started from the command line using the system-config-firewall command. Once started, the toolbar provides buttons to allow the firewall to be enabled/disabled (B). You can also configure basic trusted services, such as SSH, FTP and HTTP (C), by putting a tick in the appropriate checkbox and clicking the "Apply" button on the toolbar. The "Other Ports" section allows you to open ports that are not covered in the "Trusted Services" section. system-config-firewall
The GUI screen to control the firewall is available from the menu (System > Administration > Firewall) or can be started from the command line using the system-config-firewall command.
Once started, the toolbar provides buttons to allow the firewall to be enabled/disabled (B). You can also configure basic trusted services, such as SSH, FTP and HTTP (C), by putting a tick in the appropriate checkbox and clicking the "Apply" button on the toolbar.
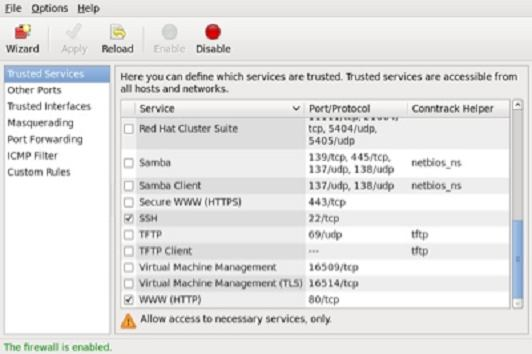
The "Other Ports" section allows you to open ports that are not covered in the "Trusted Services" section.
Question 3
Identify the Oracle-supported source for obtaining Oracle Linux
- From any good Linux distribution
- From Oracle's eDelivery software delivery cloud
- From Oracle Metalink Support
- From Linux vendors such as Red Hat or SUSE
- From Anaconda Installer
Correct answer: B
Explanation:
* Oracle Software Delivery Cloud. Here you can find downloads for the Oracle Linux Operating System, Oracle VM, and Oracle VM Templates for both Linux and Solaris. * Oracle Software Delivery Cloud. Here you can find downloads for the Oracle Linux Operating System, Oracle VM, and Oracle VM Templates for both Linux and Solaris.






