Download Oracle.1z0-134.Lead2Pass.2019-03-07.80q.tqb
| Vendor: | Oracle |
| Exam Code: | 1z0-134 |
| Exam Name: | Oracle WebLogic Server 12c: Advanced Administrator II |
| Date: | Mar 07, 2019 |
| File Size: | 2 MB |
| Downloads: | 2 |
Demo Questions
Question 1
I am configuring the security policy for my JMS module. I am specifying some security conditions for the module.
Which two security conditions are valid in this context? (Choose two.)
- The JMS module can be accessed only between 1 pm and 6 pm.
- The JMS module should throw a custom security exception on invalid access.
- The JMS module can process only 50 messages at a time.
- The JMS module can be accessed only by users belonging to the Operators group.
- The JMS module can be accessed in a receive-only mode.
Correct answer: AD
Explanation:
There are two security conditions:* time-constrained * By Group or User Reference: http://docs.oracle.com/html/E24401_02/taskhelp/jms_modules/modules/ConfigureJMSModuleSecurityPolicies.html There are two security conditions:
* time-constrained
* By Group or User
Reference: http://docs.oracle.com/html/E24401_02/taskhelp/jms_modules/modules/ConfigureJMSModuleSecurityPolicies.html
Question 2
Review the digital certificate below.
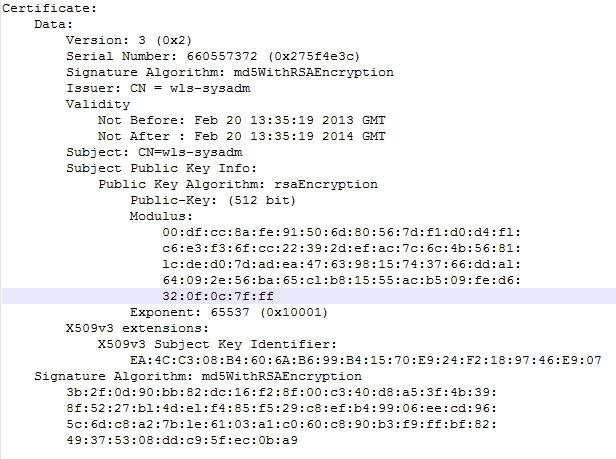
Based on what the certificate contains, which statement is true? (Choose the best answer.)
- It is a self-signed digital certificate with no certification chain.
- It is an authentic digital certificate with a valid certification chain.
- It is a digital certificate for a private key with a valid certification chain.
- It is an authentic root CA certificate with a valid certification chain.
Correct answer: A
Explanation:
Incorrect Answers:C: This is 512-bit Public Key, not a private key.Note: The subject key identifier extension provides a means of identifying certificates that contain a particular public key. Incorrect Answers:
C: This is 512-bit Public Key, not a private key.
Note: The subject key identifier extension provides a means of identifying certificates that contain a particular public key.
Question 3
You want to create a WebLogic Server (WLS) Work Manager with a Response Time Request Class of one second. You start to create the following WLST script:
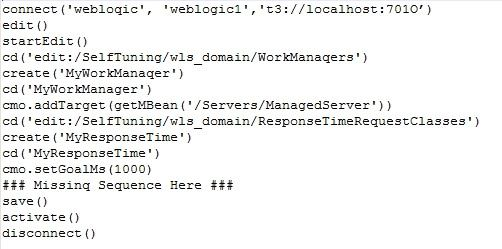
Which two can replace the missing sequence to finish this script? (Choose two.)
- cmo.addTarget(getMBean('/Servers/ManagedServer'))cd('edit:/SelfTuning/wls_domain/WorkManagers/MyWorkManager')cmo.setResponseTimeRequestClass(getMBean('/SelfTuning/wls_domain/ResponseTimeRequestClasses/MyResponseTime'))
- managedServer=getMBean('/Servers/ManagedServer')cmo.addTarget(managedServer)cmo.setWorkManaqer(getMBean('/SelfTuning/wls_domain/WorManagers/MyWorkManager'))
- cd('edit:/Servers/ManagedServer')cmo.addTarget(getMBean('/SelfTuning/wls_domain/ResponseTimeRequestClasses/MyResponseTime'))cmo.addTarget (getMBean('/SelfTuning/wls_domain/WorkManagers/MyWorkManager'))
- managedServer=getMBean('/Servers/ManagedServer')cmo.addTarget(managedServer)cd('edit:/SelfTuning/wls_domain/WorkManagers/MyWorkManager')cmo.setResponseTimeRequestClass(getMBean('/SelfTuning/wls_domain/ResponseTimeRequestClasses/MyResponseTime'))
- cmo.addTarqet('/Servers/ManagedServer')cd('/SelfTuning/wls_domain/WorkManagers/MyWorkManager')cmo.setResponseTimeRequestClass('/SelfTuning/wls_domain/ResponseTimeRequestClasses/MyResponseTime')
Correct answer: AD
Explanation:
Reference: http://docs.oracle.com/cd/E12839_01/apirefs.1111/e13952/pagehelp/J2EEappworkresponsetimerequestclassconfigtitle.html Reference: http://docs.oracle.com/cd/E12839_01/apirefs.1111/e13952/pagehelp/J2EEappworkresponsetimerequestclassconfigtitle.html






