Download Microsoft.AZ-500.PrepAway.2021-03-02.228q.tqb
| Vendor: | Microsoft |
| Exam Code: | AZ-500 |
| Exam Name: | Microsoft Azure Security Technologies |
| Date: | Mar 02, 2021 |
| File Size: | 20 MB |
Demo Questions
Question 1
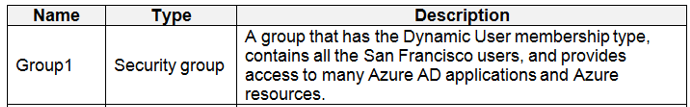
You need to meet the identity and access requirements for Group1.
What should you do?
- Add a membership rule to Group1.
- Delete Group1. Create a new group named Group1 that has a group type of Office 365. Add users and devices to the group.
- Modify the membership rule of Group1.
- Change the membership type of Group1 to Assigned. Create two groups that have dynamic memberships. Add the new groups to Group1.
Correct answer: B
Explanation:
Incorrect Answers:A, C: You can create a dynamic group for devices or for users, but you can't create a rule that contains both users and devices. D: For assigned group you can only add individual members.Scenario: Litware identifies the following identity and access requirements: All San Francisco users and their devices must be members of Group1. The tenant currently contain this group: References:https://docs.microsoft.com/en-us/azure/active-directory/users-groups-roles/groups-dynamic-membershiphttps://docs.microsoft.com/en-us/azure/active-directory/fundamentals/active-directory-groups-create-azure-portal Incorrect Answers:
A, C: You can create a dynamic group for devices or for users, but you can't create a rule that contains both users and devices.
D: For assigned group you can only add individual members.
Scenario:
Litware identifies the following identity and access requirements: All San Francisco users and their devices must be members of Group1.
The tenant currently contain this group:
References:
https://docs.microsoft.com/en-us/azure/active-directory/users-groups-roles/groups-dynamic-membership
https://docs.microsoft.com/en-us/azure/active-directory/fundamentals/active-directory-groups-create-azure-portal
Question 2
You need to ensure that the Azure AD application registration and consent configurations meet the identity and access requirements.
What should you use in the Azure portal? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Correct answer: To work with this question, an Exam Simulator is required.
Explanation:
Reference:https://docs.microsoft.com/en-us/azure/active-directory/manage-apps/configure-user-consent Reference:
https://docs.microsoft.com/en-us/azure/active-directory/manage-apps/configure-user-consent
Question 3
You need to ensure that User2 can implement PIM.
What should you do first?
- Assign User2 the Global administrator role.
- Configure authentication methods for contoso.com.
- Configure the identity secure score for contoso.com.
- Enable multi-factor authentication (MFA) for User2.
Correct answer: A
Explanation:
To start using PIM in your directory, you must first enable PIM. 1. Sign in to the Azure portal as a Global Administrator of your directory. You must be a Global Administrator with an organizational account (for example, @yourdomain.com), not a Microsoft account (for example, @outlook.com), to enable PIM for a directory. Scenario: Technical requirements include: Enable Azure AD Privileged Identity Management (PIM) for contoso.com References:https://docs.microsoft.com/bs-latn-ba/azure/active-directory/privileged-identity-management/pim-getting-started Manage identity and access To start using PIM in your directory, you must first enable PIM.
1. Sign in to the Azure portal as a Global Administrator of your directory.
You must be a Global Administrator with an organizational account (for example, @yourdomain.com), not a Microsoft account (for example, @outlook.com), to enable PIM for a directory.
Scenario: Technical requirements include: Enable Azure AD Privileged Identity Management (PIM) for contoso.com
References:
https://docs.microsoft.com/bs-latn-ba/azure/active-directory/privileged-identity-management/pim-getting-started
Manage identity and access






