Download Fortinet.NSE4_FGT-6.0.CertKiller.2019-12-05.75q.tqb
| Vendor: | Fortinet |
| Exam Code: | NSE4_FGT-6.0 |
| Exam Name: | Fortinet NSE4 - FortiOS 6.0 |
| Date: | Dec 05, 2019 |
| File Size: | 5 MB |
Demo Questions
Question 1
What files are sent to FortiSandbox for inspection in flow-based inspection mode?
- All suspicious files that do not have their hash value in the FortiGuard antivirus signature database.
- All suspicious files that are above the defined oversize limit value in the protocol options.
- All suspicious files that match patterns defined in the antivirus profile.
- All suspicious files that are allowed to be submitted to FortiSandbox in the antivirus profile.
Correct answer: C
Question 2
Which statements about a One-to-One IP pool are true? (Choose two.)
- It is used for destination NAT.
- It allows the fixed mapping of an internal address range to an external address range.
- It does not use port address translation.
- It allows the configuration of ARP replies.
Correct answer: CD
Question 3
An administrator is investigating a report of users having intermittent issues with browsing the web. The administrator ran diagnostics and received the output shown in the exhibit.
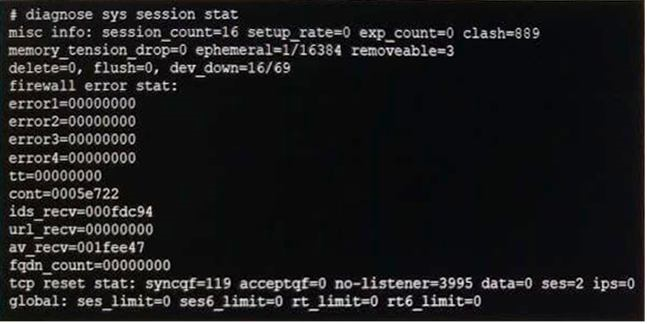
Examine the diagnostic output shown exhibit. Which of the following options is the most likely cause of this issue?
- NAT port exhaustion
- High CPU usage
- High memory usage
- High session timeout value
Correct answer: A






